Our founder, Matt Titcombe, was a volunteer on the Cyber-AB Standards Industry Working Group. He has directly participated in:
- Creation of the assessment methodology
- Creation and drafting of the CMMC Assessment Criteria
- Creation and drafting of the CMMC Getting Started guide
Mr. Titcombe is also a Subject matter Expert developing certified training curriculum for the Cyber-AB approved Licensed Partner Publishers. Specifically, he has worked on the CMMC Certified Practitioner (CCP) and Assessor (CCA) curriculums.
Per NIST SP 800-171A, an assessment or “security control assessment” means:
“The testing or evaluation of security controls to determine the extent to which the controls are implemented correctly, operating as intended, and producing the desired outcome with respect to meeting the security requirements for a system or organization.”
The CMMC Program definition in 32 CFR Part 170 defines an assessment as:
“The testing or evaluation of security controls to determine the extent to which the controls are implemented correctly, operating as intended, and producing the desired outcome with respect to meeting the security requirements for an information system or organization, as defined in §170.15 to §170.18.
Source: §170.4, Acronyms & Definitions
Keeping in mind the definition of an assessment from https://peakinfosec.com/faq-items/what-is-an-assessment/,
“The testing or evaluation of security controls to determine the extent to which the controls are implemented correctly, operating as intended, and producing the desired outcome with respect to meeting the security requirements for a system or organization.”
The key difference is the intent of the assessment. Additionally, every authorized CMMC 3rd Party Assessment Organization (C3PAO) may have tweaked definitions.
The short answer is gap assessments are used where consultative advice is given to correct identified deficiencies.
A Mock Assessment does not give any consultative advice or recommendations but is not intended to be used for a certification event. Mock Assessments are commonly used with Pre-Assessment Readiness Reviews (PARR) and Certification Assessment Readiness Reviews (CARR) prior to the form Conformity Assessment.
The Conformity Assessment is the formal event led by a C3PAO or Defense Industrial Base Cybersecurity Assurance Center (DIBCAC) assessors that results in a formal scoring and submission to formal reporting mechanisms like the Supplier Performance Risk System (SPRS).
Here is a table view of the differences:
| Gap | Mock | Conformity | |
| Identifies deficiencies | Yes | Yes | Yes |
| Provides recommended remediations | Yes | No | No |
| Used in consultative engagements | Yes | No | No |
| Used to gauge an organization’s readiness for a formal certification event | No | Yes | No |
| Used in a JSVA | No | No | Yes |
| Used for a CMMC formal assessment | No | No | Yes |
| Results are submitted to SPRS | No | No | Yes |
| Results are submitted to CMMC eMASS | No | No | Yes |
As of right now, none.
Peak InfoSec is an Authorized C3PAO. However, until the 32 CFR Part 170 CMMC Program rule is formally published, CMMC technically does not exist.
Once it is published, Peak InfoSec will be re-authorized by the CyberAB and allowed to conduct CMMC Conformity Assessments.
Not Yet.
Peak InfoSec was authorized by the Cyber Accreditation Body (Cyber-AB) to be a CMMC 3rd Party Assessor Organization in May 2022. Our CMMC Accreditation Body Marketplace listing is at https://cyberab.org/Catalog#!/c/s/Results/Format/list/Page/1/Size/9/Sort/NameAscending?term=Peak%20InfoSec.
We are waiting for the Draft 32 CFR Part 170 rule to go into effect before we can conduct formal CMMC Conformity Assessments.
Peak InfoSec completed a Defense Industrial Base Cybersecurity Assurance Center (DIBCAC) CMMC assessment in April 2022 and we were certified as being fully compliant at Level 2.
Yes. Peak InfoSec can help you organization by providing:
- Assessment of your current status
- Identification of required remediations
- Helping to implement remediations
- Tailoring our CMMC Policy Package to meet your business
- Building your evidence book
- Being there during the Audit
Yes, and all will require varying degrees of tailoring to fir your business.
Our Policy & Plans package requires the least amount of tailoring while procedures will require a lot more.
Yes. Peak InfoSec is an authorized C3PAO. To be authorized, Peak InfoSec underwent a Defense Industrial Base Cybersecurity Assurance Center (DIBCAC) audit of our NIST SP 800-171 implementation and conformity to DFARS Clause 252.204-7012 Safeguarding Covered Defense Information and Cyber Incident Reporting.
Yes. Peak InfoSec is an authorized C3PAO. To be authorized, Peak InfoSec underwent a Defense Industrial Base Cybersecurity Assurance Center (DIBCAC) audit of our NIST SP 800-171 implementation. DIBCAC certified us against CMMC 2.0.
When it comes to CMMC, the formal audit is called a “Conformity Assessment,” and we refer to the gap assessment phase where we provide recommended remediations as “Consulting.”
An “Evidence Book” is created during the pre-Audit efforts and is provided to the Auditor at the start of an audit. The Auditor uses this to document to conduct their initial compliance review of your controls. Depending on the Auditor and audit requirements, the Auditor may spot check a percentage of controls or validate all are compliant. The “Evidence Book” streamlines the audit process for everyone.
Yes.
CMMC auditors will focus extra attention on your Supply Chain and your IT/MSP provider will be the first ones a good auditor will ask about.
Make sure your organization passes both the FAR 52 & DFARS Clause onto them. Don’t try to read in partial compliance…you don’t have the authority per the DFARS clause.
External Service Providers (ESP) are heavily cited as being in scope in the DRAFT 32 CFR Part 170 – Cybersecurity Maturity Model Certification (CMMC) Program rule.
In our experience working through real world Incidents with DC3, you only need to provide them the information about the confirmed or potential Indicators of Compromise.
Information about the hackers Tools, Techniques, and Procedures (TTP); business impacts; data exfiltration; and remediation efforts can be provided in your final report.
DC3 does like to get your list on DoD contracts as soon as possible.
For more information about our Incident Response Services, please go to our CMMC Incident Response page.
No.
The key word in the definition is “potential.” We also call it an “Indicator of Compromise” or IoC.
The “potential” part is wherever Confidentiality, Integrity, or Availability of the system may indicate a compromise.
The firewall or your End Point Protection software blocking malware or stopping a user from going to malicious site is not an IoC and does not need to be reported.
Remember, you need to report an Incident with 72 hours to DC3.
For more information about our Incident Response Services, please go to our CMMC Incident Response page.
We recommend clients target CMMC Level 2 because it encompasses all of the 110 controls in NIST SP 800-171.
Only DoD can direct an organization to be CMMC Level 3 Certified. It is recommended that organizations that already handle Classified artifacts, work with Space, Command and Control, or are large integrators be ready to be CMMC Level 3 certified.
Officially:
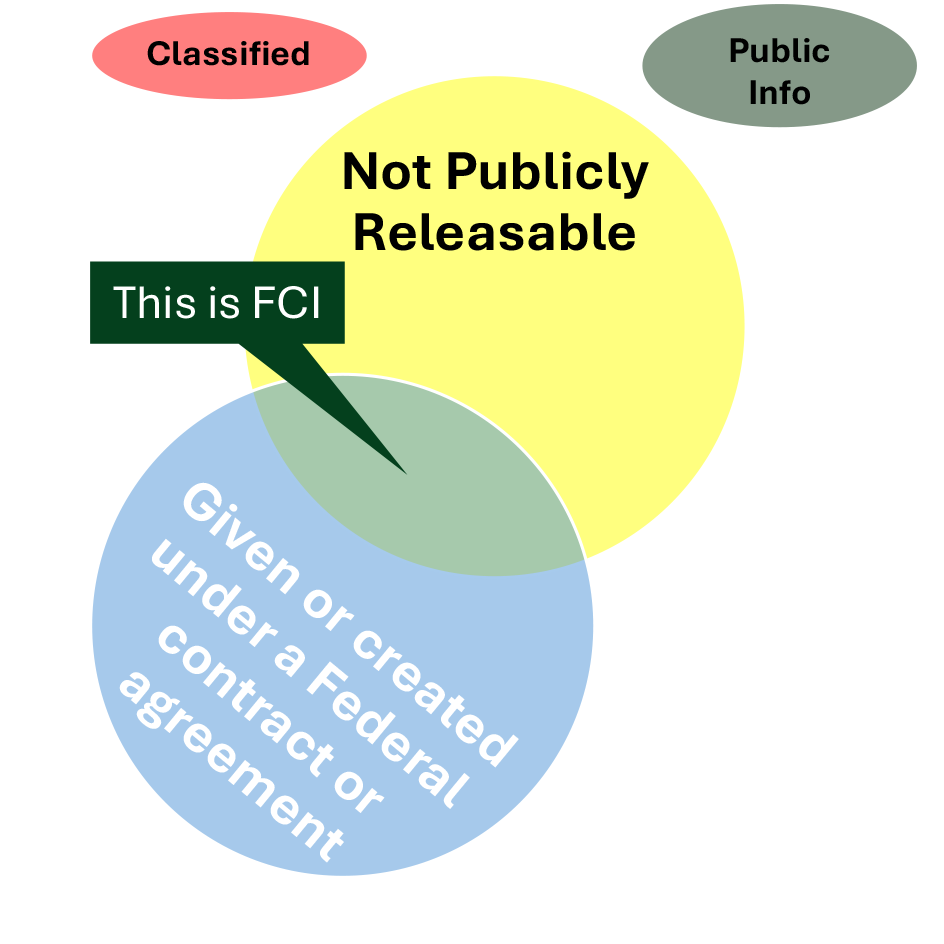
Federal Contract Information means information, not intended for public release, that is provided by or generated for the Government under a contract to develop or deliver a product or service to the Government, but not including information provided by the Government to the public (such as on public Web sites) or simple transactional information, such as necessary to process payments. Source: 48 CFR § 52.204-21
Unofficially, FCI is the lowest level of information a DoD Contractor has to protect and is only associated with CMMC Level 1. FCI occurs where information is created by either the Federal Agency or a contractor when it is information about the contract that the Federal government does not want publicly released.
FCI is not:
- Publicly available content
- Classified information
Some common examples of FCI include:
- Emails between you and your DoD Contracting Officer or Prime about the contract.
- Information you may be loading into your ERP about the contract.
For the long answer, go to “Does our organization handle Controlled Unclassified Information (CUI)? (Long Winded Answer)”
Our interpreted definition is:
Any Technical Information collected, developed, received, transmitted, used, or stored,” such as “research and engineering data, engineering drawings, and associated lists, specifications, standards, process sheets, manuals, technical reports, technical orders, catalog-item identifications, data sets, studies and analyses and related information, and computer software executable code and source code,” used or created “in support of the performance of” a DoD “contract.”
We like turn it around and ask it as question:
Since 2015, has your organization ever “Collected, developed, received, transmitted, used, or stored” any “technical information” such as “research and engineering data, engineering drawings, and associated lists, specifications, standards, process sheets, manuals, technical reports, technical orders, catalog-item identifications, data sets, studies and analyses and related information, and computer software executable code and source code” “in support of the performance of” a DoD “contract” ?
This sure sounds like an easy question, and, given the Federal government’s involvement, it isn’t.
HINT: If you want to skip the long-winded answer, go to What is Controlled Unclassified Information (CUI)?.
Step 1: Define Covered Defense Information (CDI)
The answer begins with the DFAR’s Clause 252.204-7012, Safeguarding Covered Defense Information and Cyber Incident Reporting. Paragraph (a) has two key definitions we need to bring highlight:
“Controlled Technical Information (CTI)” means technical information with military or space application that is subject to controls on the access, use, reproduction, modification, performance, display, release, disclosure, or dissemination. Controlled technical information would meet the criteria, if disseminated, for distribution statements B through F using the criteria set forth in DoD Instruction 5230.24, Distribution Statements on Technical Documents. The term does not include information that is lawfully publicly available without restrictions.
“Covered Defense Information (CDI)” means unclassified controlled technical information or other information, as described in the Controlled Unclassified Information (CUI) Registry at http://www.archives.gov/cui/registry/category-list.html, that requires safeguarding or dissemination controls pursuant to and consistent with law, regulations, and Governmentwide policies, and is—
(1) Marked or otherwise identified in the contract, task order, or delivery order and provided to the contractor by or on behalf of DoD in support of the performance of the contract; or
(2) Collected, developed, received, transmitted, used, or stored by or on behalf of the contractor in support of the performance of the contract.
So, does the DFARs clause ever define CUI, no. Nor does it clearly define the relationship between CDI & CTI.
Step 2: Define CUI
To get the official definition of CUI, we need to go to https://www.archives.gov/cui/about, which states:
Controlled Unclassified Information (CUI) is information that requires safeguarding or dissemination controls pursuant to and consistent with applicable law, regulations, and government-wide policies but is not classified under Executive Order 13526 or the Atomic Energy Act, as amended.
That really didn’t help.
Step 3: Understand NARA’s CUI categories
The second definition points us to the National Archives & Records Administration (NARA) at http://www.archives.gov/cui/registry/category-list.html to figure out this mess. If you go to the, you will see a list of categories and sub-categories like:
- Critical Infrastructure
- Defense
- Controlled Technical Information
- DoD Critical Infrastructure Security Information
- Naval Nuclear Propulsion Information
- Unclassified Controlled Nuclear Information – Defense
- Export Control
- Immigration
- Intelligence
- International Agreements
- Law Enforcement
- Legal
- Natural and Cultural Resources
- North Atlantic Treaty Organization (NATO)
- Nuclear
- Patent
- Privacy
- Proprietary Business Information
- Provisional
- Statistical
- Tax
- Transportation
What matter to us is the definition for CTI:
“Controlled Technical Information means technical information with military or space application that is subject to controls on the access, use, reproduction, modification, performance, display, release, disclosure, or dissemination. Controlled technical information is to be marked with one of the distribution statements B through F, in accordance with Department of Defense Instruction 5230.24, “Distribution Statements of Technical Documents.” The term does not include information that is lawfully publicly available without restrictions. “Technical Information” means technical data or computer software, as those terms are defined in Defense Federal Acquisition Regulation Supplement clause 252.227-7013, “Rights in Technical Data – Noncommercial Items” (48 CFR 252.227-7013). Examples of technical information include research and engineering data, engineering drawings, and associated lists, specifications, standards, process sheets, manuals, technical reports, technical orders, catalog-item identifications, data sets, studies and analyses and related information, and computer software executable code and source code.”
The italicized part is what really matters.
Step 4: Bring it all together
In short hand, CDI is the CUI Category of Defense CTI.
We find it best to bring all of this together in the form of a question:
Since 2015, has your organization ever “Collected, developed, received, transmitted, used, or stored” any “technical information” such as “research and engineering data, engineering drawings, and associated lists, specifications, standards, process sheets, manuals, technical reports, technical orders, catalog-item identifications, data sets, studies and analyses and related information, and computer software executable code and source code” “in support of the performance of” a DoD “contract” ?
If you can answer yes to this question, then your organization handled CUI, CDI, or CTI.
For more information, please contact us at [email protected].

Social Contact