By Matthew Titcombe, CISSP, CMMC Provisional Assessor Lvl 1-3, CISO, Gigit; CEO, Peak InfoSec
Not quite the normal title…. Cybersecurity Maturity Model (CMMC), Split Tunneling, and COVID.
During the pandemic, many Department of Defense (DOD) contractors’ businesses were disrupted like so many other businesses in this country: in order to accommodate mandatory stay-at-home orders, the majority of their staff moved from an office-centric model to work-from-home one. But these DoD contractors were already contending with an unrelenting fly in their ointment: struggling to meet CMMC or NIST SP 800-17 compliance requirements.
Just as the industrial revolution caused the migration of people from rural communities to cities and offices, COVID has caused the migration of workers from their offices to homes. Even as COVID hopefully winds down with vaccination and herd immunity, its impact may have significantly and permanently changed the way America and the digitized world works. Businesses have come to realize they can lower costs with workers getting their jobs done from home, and many workers want to retain some flexibility to continue to do so. If this latter trend persists, organizations will have to address what’s known as the Split Tunneling requirement and related performance issues.
This article is intended to provide an explanation of Split Tunneling and a guide for organizations trying to address it in order to meet CMMC compliance.
What is Split Tunneling?
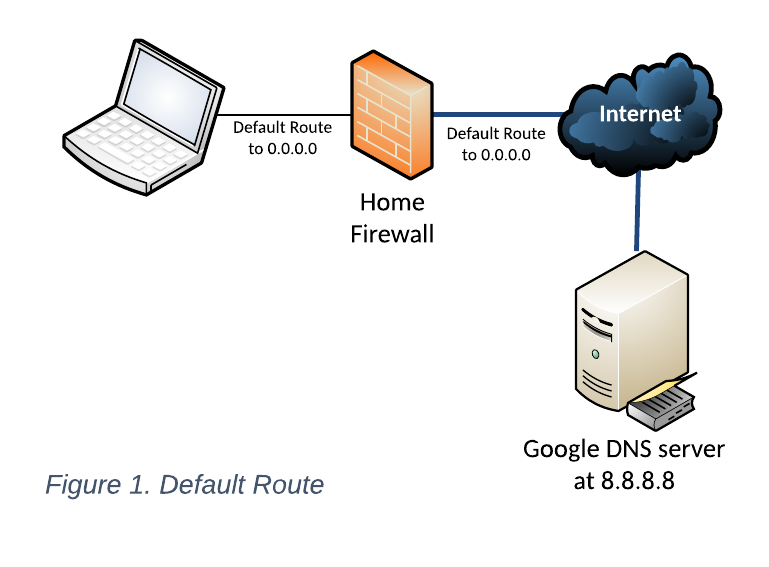 Split Tunneling is fundamentally a configuration that determines how a user connects to the Internet. As shown in Figure 1, a user’s PC and the home firewall does not know where every other system is physically connected on the internet. When it doesn’t know, it invokes the “Default Route to 0.0.0.0.” In other words, the device that doesn’t know how to connect to other devices simply passes the buck up the routing chain. Let’s say you wanted to get to one of Google’s Domain Name Servers 8.8.8.8 to resolve peakinfosec.com. Your PC would go, “I’ve got no clue how to get there. Hey Comcast Firewall (the default route for the PC), why don’t you help me get there?” The Comcast Firewall, just as clueless, then asks the Comcast router it connects to – that default route — “Can you help me get to 8.8.8.8 to resolve peakinfosec.com?” And so it goes up the chain until a router somewhere responds, “I know. Go this way.” All of this is tracked so when 8.8.8.8 says the answer is 107.180.41.44, this ultimate game of telephone tag works in reverse to get the answer back to the user’s PC.
Split Tunneling is fundamentally a configuration that determines how a user connects to the Internet. As shown in Figure 1, a user’s PC and the home firewall does not know where every other system is physically connected on the internet. When it doesn’t know, it invokes the “Default Route to 0.0.0.0.” In other words, the device that doesn’t know how to connect to other devices simply passes the buck up the routing chain. Let’s say you wanted to get to one of Google’s Domain Name Servers 8.8.8.8 to resolve peakinfosec.com. Your PC would go, “I’ve got no clue how to get there. Hey Comcast Firewall (the default route for the PC), why don’t you help me get there?” The Comcast Firewall, just as clueless, then asks the Comcast router it connects to – that default route — “Can you help me get to 8.8.8.8 to resolve peakinfosec.com?” And so it goes up the chain until a router somewhere responds, “I know. Go this way.” All of this is tracked so when 8.8.8.8 says the answer is 107.180.41.44, this ultimate game of telephone tag works in reverse to get the answer back to the user’s PC.
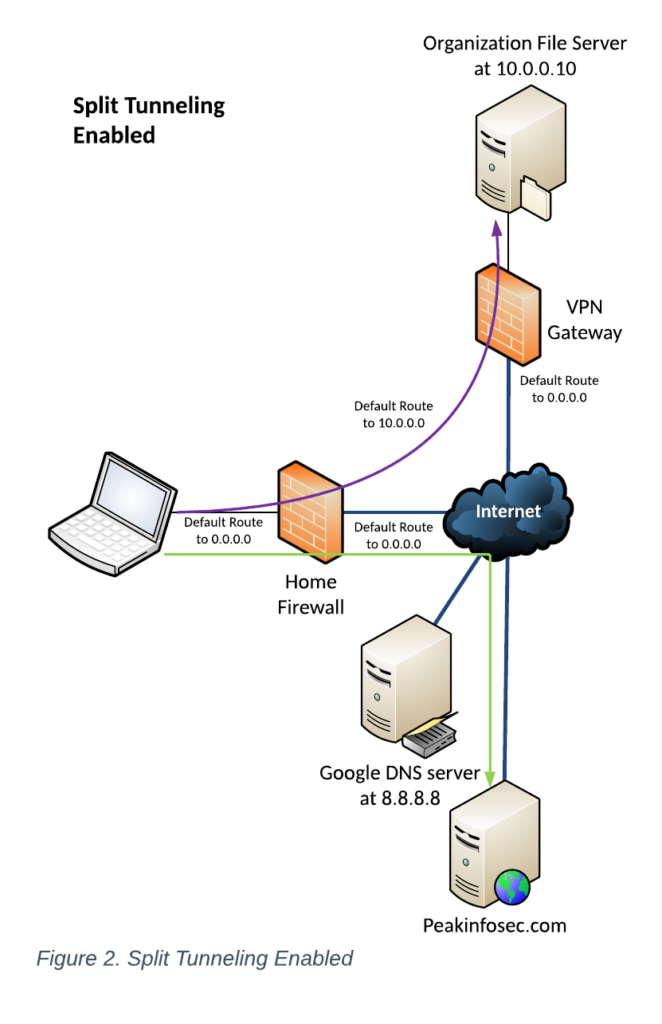 The user then connects to a Virtual Private Network (VPN) Gateway to get to the office file server. Once the VPN tunnel is established, the VPN Gateway tells the remote PC, “Hey, when you want to get to anything with a 10.0.0.x address, come up this tunnel.”
The user then connects to a Virtual Private Network (VPN) Gateway to get to the office file server. Once the VPN tunnel is established, the VPN Gateway tells the remote PC, “Hey, when you want to get to anything with a 10.0.0.x address, come up this tunnel.”
With the tunnel established, when the user wants to get to the file server at 10.0.0.10, the PC now ignores the default route out the Internet and sends all requests to 10.0.0.10 up the VPN Tunnel (the curved purple line in Figure 2). But when the user then wants to view other pages at peakinfosec.com, this time since the PC knew to send the traffic to the Comcast firewall, it follows its configuration and sends normal Internet traffic out the normal Comcast firewall route (the green right-angled line) and does not send it up the VPN tunnel.
Split Tunneling Enabled
In other words, Split Tunneling is enabled when the two following criteria occur:
- Any traffic to the IP address(es) advertised by the VPN Gateway are routed up the VPN Tunnel;
- The Default Route remains the same and traffic to any address(es) not advertised by the VPN Gateway go directly out the local firewall to the Internet.
Split Tunneling Disabled
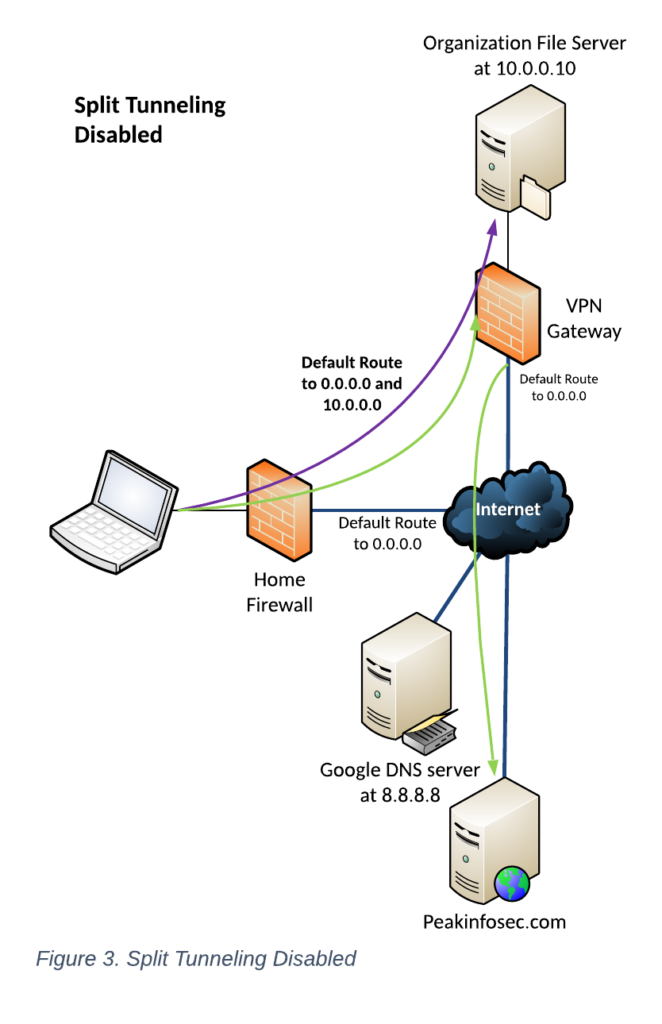
When Split Tunneling is disabled, the VPN gateway gets bossy. When the VPN tunnel is established, the VPN Gateway tells the remote PC, “Hey, I’m now your Default Route and all traffic needs to come up to me, including when you want to get to anything with a 10.0.0.x address, come up this tunnel.”
So, when the user wants to get to the fileserver, nothing has changed. However, when the user wants to get to peakinfosec.com, the traffic is routed up the tunnel to the VPN Gateway, which then sends the request out its Default Route to the Internet and eventually to the webserver.
When Split Tunneling is disabled and has the following key attributes:
- Any traffic to the IP address(es) advertised by the VPN Gateway has routed up the VPN Tunnel;
- The Default Route now equals the remote VPN Gateway and all internet traffic goes through the VPN Gateway to the Internet
“Hybrid Mode”
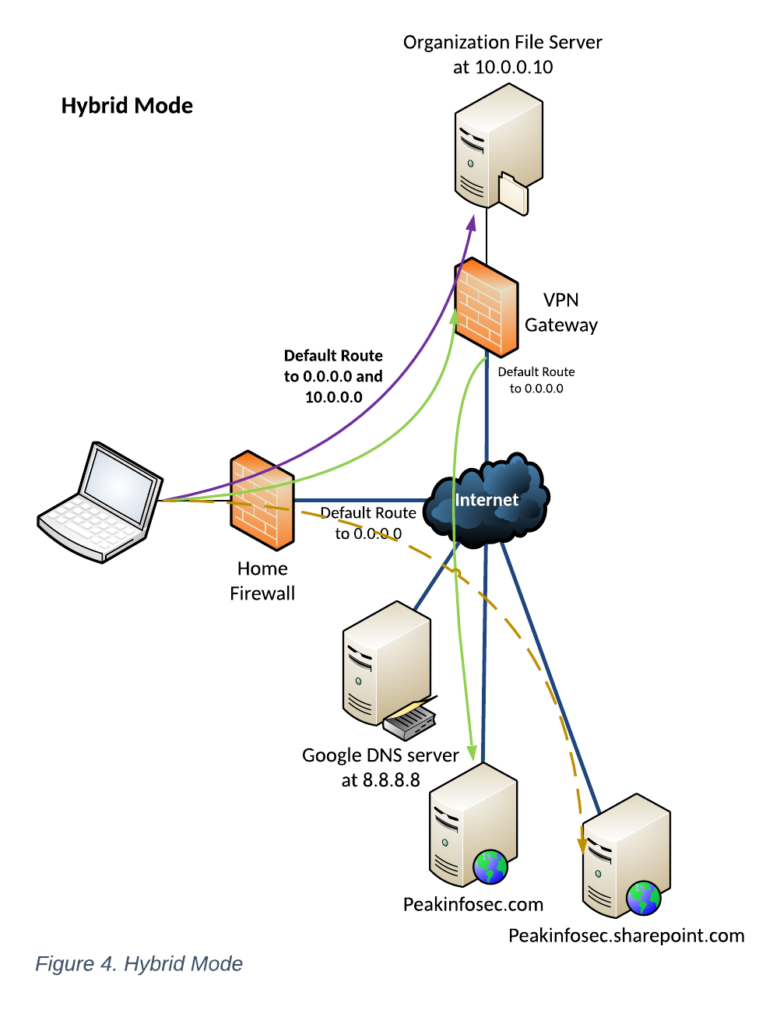
Hybrid mode is a relatively new feature for VPN Gateways and their clients. In Hybrid Mode – sometimes called “Optimized Mode” — the VPN Gateway is “less bossy.”
In this case, when the VPN tunnel is established, the VPN Gateway tells the remote PC, “Hey, I am now your Default Route, and all traffic needs to come up to me, including when you want to get to anything with a 10.0.0.x address.” It then adds, “I trust peakinfosec.sharepoint.com, so you can use your normal Default Route when going there.”
When using Hybrid Mode, the main change is that when the user wants to go to peakinfosec.sharepoint.com, the user’s traffic can go out its normal Default Path via the Comcast router and directly to the server without going through the VPN Gateway (gold dashed line in Figure 4).
Hybrid Mode has the following key attributes:
- Any traffic to the IP addresses advertised by the VPN Gateway is routed up the VPN Tunnel;
- Any sanctioned destinations are allowed to go out the normal default route through the local firewall;
- The Default Route now equals the remote VPN Gateway, and all internet traffic goes through the VPN Gateway to the Internet.
What is the Information Security Requirement regarding Split Tunneling?
Per NIST SP 800-171 Rev 2 3.13.7 and CMMC SC.3.184, the requirement is:
Prevent remote devices from simultaneously establishing non-remote connections with organizational systems and communicating via some other connection to resources in external networks (i.e., split tunneling).
Exactly what does this mean? Let’s clarify it by defining some key terms:
- Remote devices: In the figures above, the remote device is the laptop PC being used by the organization’s staff person when they are not at their normal operating location. Pre-COVID, this condition existed mainly when a person was teleworking at home for a brief duration or when they were on the road. Do not read into this with, “Why don’t we just declare their home office the normal location?” That opens a HUUUGE can of worms because their home office then requires equivalent protections as your normal office space.
- Organizational Systems: These are all the other systems that are in your system scope per NIST SP 800-171 para 1.1.
- Non-remote connections with organizational systems: When the VPN tunnel is established, it creates an encrypted connection between the gateway and the user device that allows the remote device access to internal resources as if it was in the office. This is what makes the VPN tunnel a non-remote connection.
- External Networks: External networks are any networks not under the organization’s direct or contracted control. As an example, connecting from a PC in the office (internal directly controlled network) through the Internet (external network) to peakinfosec.com (internal contracted network) traverses dozens on network spaces managed by businesses the organization may not have any control of. Likewise, going to any general Internet site (e.g., cmmcab.org) leads to an external network and external information system (c.f., AC.1.003)
To translate this requirement into layman’s terms: A company user, when not working in the office on the organization’s internal network, cannot access both internal assets via VPN services and external, untrusted information systems unless it goes through the organization’s firewalls.
In short, in order to meet the necessary requirement, Split Tunneling must be disabled.
Why do we have this requirement?
The impetus for this requirement comes down to hackers.
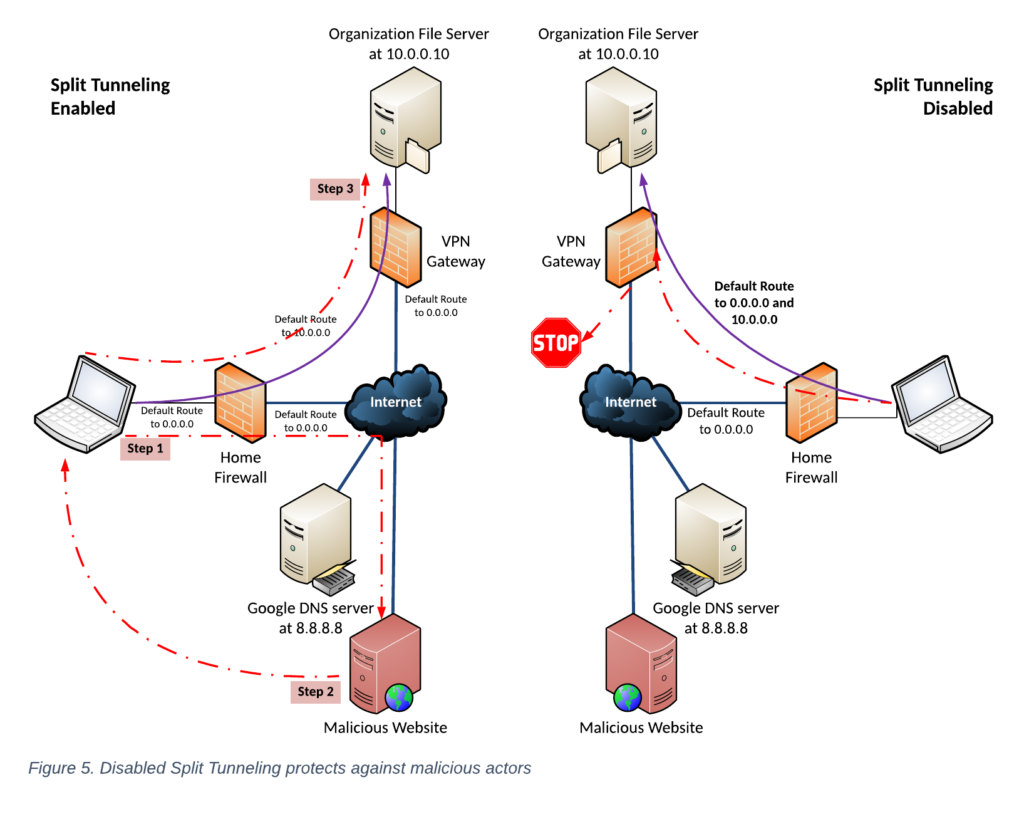
As shown on the left side of Figure 5, when Split Tunnelling is enabled, if a user connects to a malicious website (Step 1), the remote hacker can compromise the laptop (Step 2). The hacker then realizes there is a remote connection to the laptop’s organization. The hacker exploits that remote connection (Step 3) to exfiltrate data or try to break into and control the organization’s systems internally.
As shown on the right side of the diagram, when Split Tunneling is disabled, if the user tries to go to the malicious web site, the user’s traffic goes up the VPN tunnel, and hopefully the VPN Gateway’s firewall either blocks the traffic prior to the user connecting or the firewall detects the malicious traffic patterns and blocks the connection from going any further.
What are the impacts of this requirement?
When Split Tunneling is disabled, the user takes the “long way.” Instead of taking the shortest route through the Internet to get to the final destination, say peakinfosec.com, the user’s communications now have to go up to the VPN Gateway and then out the VPN Gateway’s firewall to peakinfosec.com. This is very analogous to driving the long way to the grocery store.
To make matters worse, the VPN Gateway can become a traffic jam. Now with everyone working from home and trying to connect to internal resources and getting to other Internet resources, everyone’s traffic is going through that one pipe to access everything. Your IT staff did not design your VPN Gateway for this volume. IT only sized your Internet connection for users to access the file server from inside the network and a limited number of people accessing content remotely.
Going back the trip to the grocery store analogy, now the remote users aren’t just taking a long way, they are being forced to drive through a traffic jam!
Where do we see the impact the most? Real-time services like Teams or WebEx meetings where voice or video is being shared will likely be negatively affected first. This long path causes delays, garbled communication, and even users to be dropped from the meeting.
Users will also complain that accessing internal resources is slower than when they are on-premises. Frankly, this is a normal reality no matter what, but it’s worsened with everyone trying to go through the VPN Gateway. Why? Well, at-home users typically have a smaller pipe and are competing for the bandwidth needed for other digital connections like online schooling, streaming video, and online video games. Even before COVID, it was normal to hear users complain about remote VPN performance. The traffic jam at the VPN Gateway now adds another slowdown. In the office, most users have a 1-gigabit direct connection to the file server or other internal resource, and the system is tuned for that operation.
How can an organization mitigate its effects & remain compliant?
Let’s assume your organization needs Remote User VPN and it can’t support hybrid mode. Let’s also assume your organization does not purposely do something that is non-compliant, which would leave your business open to a False Claims Act charge. Given these constraints, organizations could look to these mitigation strategies:
Option 1. Go Cloud First
This is our model. We don’t use Remote User VPN at all. All of our information and services are hosted up our Microsoft Government Community Cloud – High (GCCH) Office 365 (O365) tenant. Since our GCCH O365 tenant is considered a part of our system and internal, we leverage all of the benefits of the O365 cloud without the headaches of having on-premises servers.
This model does not work for a sizeable portion of the Defense Industrial Base, especially those in manufacturing and Research & Development. These types of firms need access to on-premises systems when users remote.
Option 2. Upgrade to a VPN Solution that Supports Hybrid Mode
The other option is to replace the VPN Gateway with one that can handle hybrid mode. Frankly, Palo Alto Networks led this innovation and has one of the best but most expensive solutions. All VPN Gateway and Next-Generation Firewall vendors are adding this capability.
We’d only recommend this to a client if the performance issues are so bad they really are affecting the bottom line. We say this because the cost of replacement is not just the new device but all the hours to set it up and re-configure it for the organization.
We’d also caution the business before making this change if they intend to have staff return to the office after the pandemic subsides.
Option 3. Grin and Bear It
For SMBs in particular, this is the most common option. When we hit this option, we recommend manual strategies where possible. For example, when a user needs to join a Teams meeting and doesn’t need access to internal resources during the meeting, drop the VPN connection. We also recommend using dial-in phone numbers versus using the computer’s microphone and speakers.
The other manual approach is to not have users surf the web while connected to the VPN.
In Summary
COVID has forced us to relook at how we operate, and as a result, many of the presumptions we had regarding how things work in an office don’t function with everyone working from home. Unfortunately, technology is having to keep up with the changes COVID has caused. While it may not make sense to change VPN Gateways now, make sure future Firewall and VPN Gateway purchases support hybrid Tunneling mode.


Social Contact