Our Approach
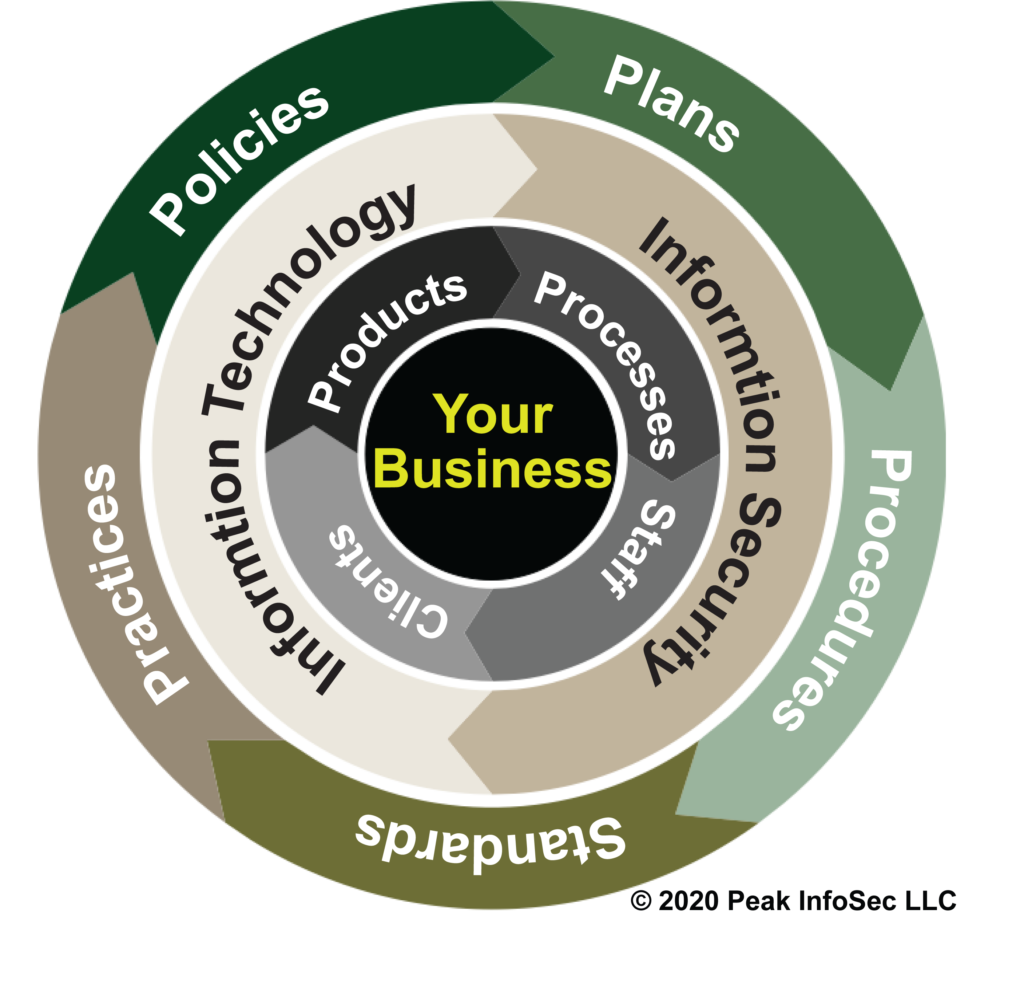
At the core of every Peak InfoSec service is the diagram to the right. Whether we are helping to shape your organization’s culture, implement nontechnical or technical controls, it always come back to putting in place effective Policies, Plans, Procedures, Standards & Practices (4PS).
Why? Our founder picked up the 4PS from his doctor during one of their rabbit-hole discussions. He explained a doctor’s practice is when the doctor is working to help the patient. Prior to that, they follow policies (e.g., prioritization of patient criticality), plans for things like patient having a heart attack, and then specific procedures to execute a policy or plan. All of these actions are based on standards set by the medical boards. We then judge how well they practices this. BTW, this is why a doctor’s business is called a “Practice.”
That made sense and Peak InfoSec adopted the approach to Information Security practices. At the center of the 4PS are the core components of your business. Those in turn are being supported by your Information Security and Technology services.
The 4PS are the mechanism that drives your organizations culture.
Accept No Network is 100% Securable
Suffice it to say, all companies, including the Federal government, are not willing to secure their networks 100% of the time. As a mathematician, our Founder Matt Titcombe proved in a paper submitted to the Air Force Institute of Technology that the best Information Security and Technology teams in the world have a better chance to win the lottery than to perfectly secure your network. It boils down to a simple reality, no one has enough money, time, and skilled employees to secure an incredibly complex network completely as conditions change.
To make matters worse, EVERY software manufacturer that you use from Amazon to Microsoft to Zebra has new and changing vulnerabilities in their systems that hackers continually seek to identify and exploit.
By following our approach, we account for the inherent insecurity of every network.
When the likelihood of your organization, given enough time, to suffer a significant Information Security incident is 100%, our goal is to then reduce frequency and impact when in incident occurs.


Prioritize your Information Assets and Risk Exposures
In this process step, we assess your company from three perspectives:
Business Operations: Peak InfoSec will assess what business processes are key to your organization; what types of information assets your firm uses; and, what your legal and regulatory drivers for information security (e.g., Payment Card Industry Data Security Standard (PCI DSS)) are.
Existing 4PS: We assess your organization’s existing 4Ps: Plans, Policies, Procedures, Standards & Practices.
Technical Audit: Peak InfoSec will perform an IT architecture audit of your infrastructure to identify risk exposure areas, software vulnerabilities, and technical gaps in best practices for information security.
The result of this methodology is a complete risk assessment for your firm based on a snapshot in time.
Develop the “4PS”
The 4Ps are the blueprint by which we will work with your company to reduce your Information Security Risk Exposure. We will develop your:
Policies: The Policies are defined, written, and published for all to follow. Policies range from standards your IT personnel will follow to end-user usage policies. Many policies then get translated into technical controls applied to your Information Systems.
Plans: The Plan or set of plans can begin as high-level as an Enterprise Architecture or be as discrete as a Continuity of Operations Plan.
Procedures: Procedures are the documented standard processes your company will follow to protect itself from your internal and external risks.
Standards: Standards set everything from Password complexity to acceptable data loss levels for your organization.
Practices: Practices are where this becomes real. Practices are how well your organization is executing your Policies, Plans, Procedures, & Standards.
All of these and the results from the previous process step converge into our assessment report that your organization can use to guide remediation actions.


Mature the “4PS”
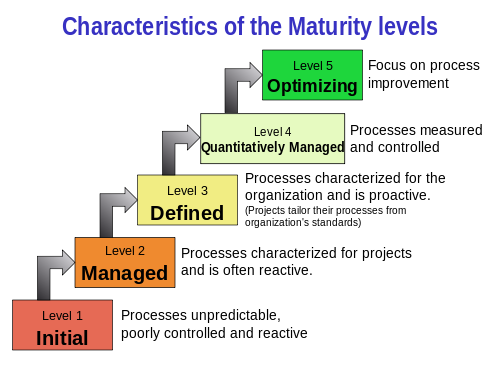
Members of industry, government and the Carnegie Mellon Software Engineering Institute (SEI) developed the Capability Maturity Model Integration (CMMI) paradigm.
Our goal at Peak InfoSec is to help your company mature your Information Technology supported processes and systems from the Initial Level 1 phase to becoming managed and repeatable (Level 4).

Social Contact