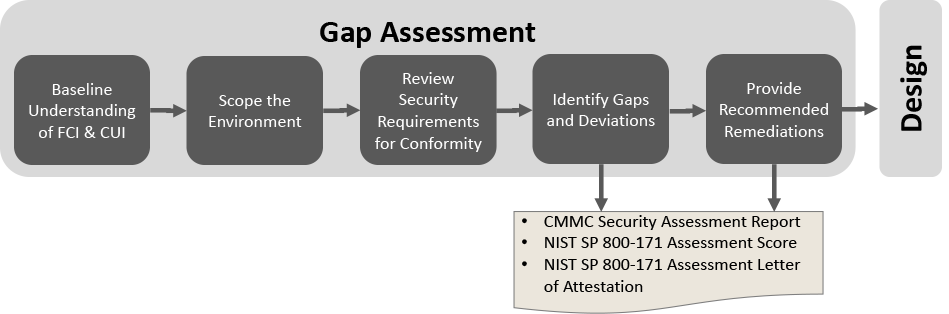
Consulting Phase 1: Gap Assessment
Whether your organization is targeting CMMC Level 1, 2, or 3, our Consulting Phase 1, Gap Assessment is designed to identify and understand deficiencies that would hinder you achieving a full certification. As we conduct your Gap Assessment, we are following the NIST SP 800-171 definition for an Assessment:
“The testing or evaluation of security controls to determine the extent to which the controls are implemented correctly, operating as intended, and producing the desired outcome with respect to meeting the security requirements for a system or organization.”
A deficiency is then where “the controls are not implemented correctly, operating as intended, or producing the desired outcome with respect to meeting the security requirements for a system or organization.”
Step 1: Baseline Understanding of FCI & CUI
 In Step 1, Baseline Understanding of Federal Contract Information (FCI) & Controlled Unclassified Information (CUI) invariably brings us to the Five Kids.
In Step 1, Baseline Understanding of Federal Contract Information (FCI) & Controlled Unclassified Information (CUI) invariably brings us to the Five Kids.
Why? Fundamentally, the Security Requirements to safeguard FCI & CUI are information-centric versus system-centric. So, wherever FCI & CUI goes, that establishes your scope. Back to the Five Kids…the mud that covers them is the FCI & CUI in your business. No matter how much you hose those Five Kids down, they are going to track mud into your home.
Our first step is to help an organization understand FCI and the types of CUI they likely have within their enterprise. We also help them to develop a working definition for the types of CUI they have.
Step 2: Scope the Environment
In step 2, Scope the environment, we follow the Five Kids. Specifically, we work with your organization to:
- Identify all contracts with FAR 52.204-21, DFARS Clause 252.204-7008, DFARS Clause 252.204-7012, or DFARS Clause 252.204-7020 in them.
- Identify all processes involved with the contract(s) from bidding to closeout.
- Identify all people and facilities used in those processes.
- Identify all IT systems used by those people and facilities.
- Identify all the IT Components that process, store, or transmit CUI or “looks like CUI”.
- Identify the Security Protection components that protect the CUI-related IT system components.
- Identify all other Security protection components.
- Document all processes, people, facilities, and technologies in your scope diagram.
We use our Scope Diagram Template in this step to keep track of all this. You can also find out more about this step by watching:
Step 3: Review Security Requirements for Conformity
 When evaluating your organization’s conformity to NIST SP 800-171 in a gap assessment, we work at the Assessment Objective to System Component level.
When evaluating your organization’s conformity to NIST SP 800-171 in a gap assessment, we work at the Assessment Objective to System Component level.
During the formal Conformity Assessment, a C3PAO or DIBCAC assessor is evaluating against all 320 Assessment Objectives identified in NIST SP 800-171A, Assessing Security Requirements for Controlled Unclassified Information. In doing their examinations, interviews, or tests, the Assessor will pull a random sample from all of your components in scope. Components are not limited to Information Technology assets. A component can be:
- A person;
- A process;
- A technology; or
- A Facility.
During a Conformity Assessment, if one Component is NOT MET, then the related Assessment Objective is NOT MET, and per CMMC guidance, the Security requirement is NOT MET.
Step 4: Identify Gaps and Deviations
As we work through your Assessment Objective to System Component level implementations, we will identify deficiencies. That is the ultimate goal of Step 4, Identify Gaps and Deviations. As we do this, your organization and team members will begin to suffer the CMMC Seven Stages of Grief.
This is normal as we identify and correct misconceptions about the Security Requirements and Assessment Objectives. The misconceptions do lead to incorrect implementations that also get added to the database we use to track all of this. Where possible, we try to associate the non-compliant component if it is an exception. Many times, the deficiency is a complete gap that spans all components of that type.
Step 4: Provide Recommended Remediations
For each deficiency we identify in Step 4, we will identify at least one and most times multiple recommended remediations that will need to be implemented to correct the issues.
The list of recommended remediations is like a grocery list of all the things that need to get done. It is very common when organizations see their complete list of deficiencies and recommended remediations to get overwhelmed. As one of the first stages of the CMMC Seven Stages of Grief, we are experts in walking organizations out of being overwhelmed.
Consulting Phase 1: Gap Assessment Deliverables
Peak InfoSec provides the following deliverables as a part of Phase 1: Gap Assessment:
- CMMC Security Assessment Report (CSAR): This report provides summary and detailed conformity for all Security Requirements and Assessment Objectives. We also identify all applicable deficiencies and recommended remediations for each NOT MET Security Requirement.
- NIST SP 800-171 Assessment Score: Using the DoD Assessment Methodology (DoDAM), we calculate your Supplier Performance Risk System score from NIST SP 800-171 compliance.
- NIST SP 800-171 Assessment Letter of Attestation: We also provide your organization a digitally signed Letter of Attestation stating you have engaged an Authorized C3PAO who conducted a Conformity Assessment of your environment.
If we continue to provide consulting services to your organization, we use all the deliverables above as we enter into Consulting Phase 2: Design and Plan and then later on in Consulting Phase 3: Remediation.

Social Contact