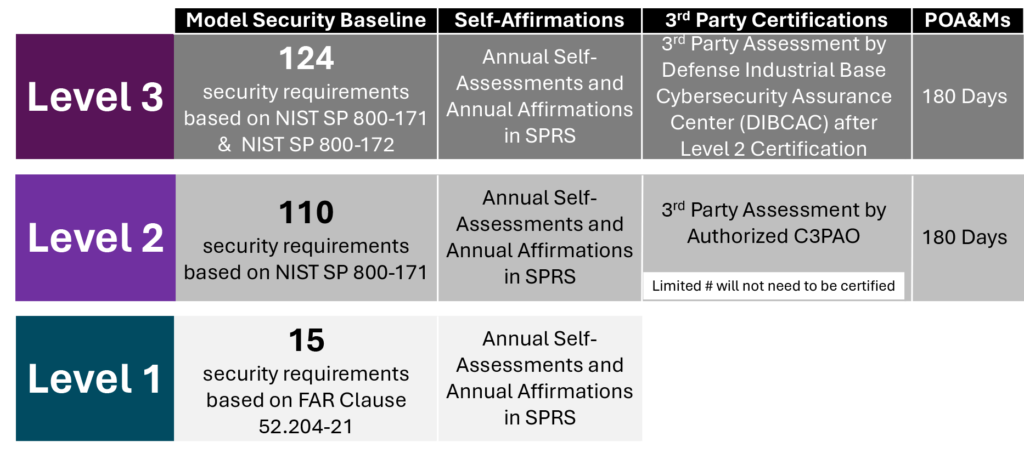
CMMC Level 3 Conformity Assessments
CMMC Level 3 Conformity Assessments are supplemental to CMMC Level 2 conformity requirements and certifications by an Authorized CMMC 3rd Party Assessment Organization (C3PAO). Out of all the 39 enhanced Security Requirements in NIST SP 800-172 Enhanced Security Requirements for Protecting Controlled Unclassified Information: A Supplement to NIST Special Publication 800-171, DoD has chosen to require 24.
CMMC Level 3 Model Baseline
Per the Draft rule, and specifically Table 1 to § 170.14(c)(4), the 24 Level 3 Security Requirements are:
- L3–3.1.2e, Restrict access to systems and system components to only those information resources that are owned, provisioned, or issued by the organization.
- AC.L3–3.1.3e, Employ secure information transfer solutions to control information flows between security domains on connected systems.
- AT.L3–3.2.1e, Provide awareness training upon initial hire, following a significant cyber event, and at least annually, focused on recognizing and responding to threats from social engineering, advanced persistent threat actors, breaches, and suspicious behaviors; update the training at least annually or when there are significant changes to the threat.
- AT.L3–3.2.2e, Include practical exercises in awareness training for all users, tailored by roles, to include general users, users with specialized roles, and privileged users, that are aligned with current threat scenarios and provide feedback to individuals involved in the training and their supervisors.
- CM.L3–3.4.1e, Establish and maintain an authoritative source and repository to provide a trusted source and accountability for approved and implemented system components.
- CM.L3–3.4.2e, Employ automated mechanisms to detect misconfigured or unauthorized system components; after detection, remove the components or place the components in a quarantine or remediation network to facilitate patching, re-configuration, or other mitigations.
- CM.L3–3.4.3e, Employ automated discovery and management tools to maintain an up-to-date, complete, accurate, and readily available inventory of system components.
- IA.L3–3.5.1e, Identify and authenticate systems and system components, where possible, before establishing a network connection using bidirectional authentication that is cryptographically based and replay resistant.
- IA.L3–3.5.3e, Employ automated or manual/procedural mechanisms to prohibit system components from connecting to organizational systems unless the components are known, authenticated, in a properly configured state, or in a trust profile.
- IR.L3–3.6.1e, Establish and maintain a security operations center capability that operates 24/7, with allowance for remote/on-call staff.
- IR.L3–3.6.2e, Establish and maintain a cyber-incident response team that can be deployed by the organization within 24 hours.
- PS.L3–3.9.2e, Ensure that organizational systems are protected if adverse information develops or is obtained about individuals with access to CUI.
- RA.L3–3.11.1e, Employ threat intelligence, at a minimum from open or commercial sources, and any DoD-provided sources, as part of a risk assessment to guide and inform the development of organizational systems, security architectures, selection of security solutions, monitoring, threat hunting, and response and recovery activities.
- RA.L3–3.11.2e, Conduct cyber threat hunting activities on an on-going aperiodic basis or when indications warrant, to search for indicators of compromise in organizational systems and detect, track, and disrupt threats that evade existing controls.
- RA.L3–3.11.3e, Employ advanced automation and analytics capabilities in support of analysts to predict and identify risks to organizations, systems, and system components.
- RA.L3–3.11.4e, Document or reference in the system security plan the security solution selected, the rationale for the security solution, and the risk determination.
- RA.L3–3.11.5e, Assess the effectiveness of security solutions at least annually or upon receipt of relevant cyber threat information, or in response to a relevant cyber incident, to address anticipated risk to organizational systems and the organization based on current and accumulated threat intelligence.
- RA.L3–3.11.6e, Assess, respond to, and monitor supply chain risks associated with organizational systems and system components.
- RA.L3–3.11.7e, Develop a plan for managing supply chain risks associated with organizational systems and system components; update the plan at least annually, and upon receipt of relevant cyber threat information, or in response to a relevant cyber incident.
- CA.L3–3.12.1e, Conduct penetration testing at least annually or when significant security changes are made to the system, leveraging automated scanning tools and ad hoc tests using subject matter experts.
- SC.L3–3.13.4e, Employ physical isolation techniques or logical isolation techniques or both in organizational systems and system components.
- SI.L3–3.14.1e, Verify the integrity of security critical and essential software using root of trust mechanisms or cryptographic signatures.
- SI.L3–3.14.3e, Ensure that Specialized Assets including IoT, IIoT, OT, GFE, Restricted Information Systems, and test equipment are included in the scope of the specified enhanced security requirements or are segregated in purpose-specific networks.
- SI.L3–3.14.6e, Use threat indicator information and effective mitigations obtained from, at a minimum, open or commercial sources, and any DoD-provided sources, to guide and inform intrusion detection and threat hunting.
These are in addition to the previously C3PAO certified Security Requirements form CMMC Level 2.
CMMC Level 3 Self-Affirmation Requirements
§170.18, CMMC Level 3 Certification Assessment and Affirmation requirements established the self-affirmation requirements for organizations that need to be CMMC Level 3 conformant.
Organizations that need to be at CMMC Level 3 will need to measure their conformity annually against the related Assessment Objectives in NIST SP 800-172A, Assessing Enhanced Security Requirements for Controlled Unclassified Information.
CMMC Level 3 organizations will need to submit a separate Self-Affirmation annually for their Level 3 environment if it is an enclave within their Level 2 environment. If not, the organization can submit a single self-affirmation letter for their combined CMMC Level 2 & 3 environment. Organizations may want to have their Authorized C3PAO support them for their annual reviews.
CMMC Level 3 Third Party Certification Requirements
Organizations that need to be CMMC Level 3 must be fully certified at CMMC Level 2 by an Authorized C3PAO before being eligible for a CMMC Level 3 Conformity Assessment.
CMMC Level 3 Conformity Assessments are conducted by the Defense Industrial Base Cybersecurity Assessment Center (DIBCAC) (c.f., §170.18(a)(1)). Authorized C3PAOs will not conduct Level 3 Conformity Assessments.
CMMC Level 3 Plans of Action & Milestones (POA&M)
Conditional POA&Ms are allowed for CMMC Level 3 with the following restrictions being met:
- The number of MET CMMC Level 3 requirements must be equal to or greater than 20.
- The POA&M does not include any of the following security requirements:
- IR.L3–3.6.1e Security Operations Center.
- IR.L3–3.6.2e Cyber Incident Response Team.
- RA.L3–3.11.1e Threat-Informed Risk Assessment.
- RA.L3–3.11.6e Supply Chain Risk Response.
- RA.L3–3.11.7e Supply Chain Risk Plan.
- RA.L3–3.11.4e Security Solution Rationale.
- SI.L3–3.14.3e Specialized Asset Security.
Conditional POA&Ms must be closed out within 180 days of the initial self-assessment or DIBCAC Conformity Assessment.
Peak InfoSec Provided Services
Even as an Authorized C3PAO, Peak InfoSec cannot conduct your CMMC Level 3 Conformity Assessment, Peak InfoSec can support your organization with the following services:
- CMMC Level 3 Mock Assessments: Peak InfoSec can conduct a Mock Assessment of your Level 3 Assessment. Our experience sitting across the table from DIBCAC assessors during non-voluntary assessments as well as sitting with them during Joint Surveillance Voluntary Assessments (JSVA) as an Authorized C3PAO will bring the same level of rigor DIBCAC will use.

Social Contact